How to get my wallet address to deposit crypto?
Ligamos para si gratuitamente
Usa Payday Loans In Kansas Online, No Credit Check, No Fax Needed, 3 Minutes!
24 Junho, 2022Кредит наличными с плохой кредитной историей в Таразе Экспресс кредитвзять наличнымив Таразе
14 Julho, 2022How to get my wallet address to deposit crypto?
Content
- How to get my wallet address to deposit crypto?
- Vacation season: How to travel safely with cryptocurrencies
- How to Choose the right Cryptocurrency to Trade or Invest in
- The Keys to Crypto Kingdom: Wallet Address, Public and Private Keys Explained
- Core Functionality
- What is a Crypto Wallet?
- Cryptocurrency Wallet: What It Is, How It Works, Types, Security
- How much do you know about Bitcoin?
At times, users need to move keys from one wallet to another—to upgrade or replace the wallet software, for example. Private key backups might also be stored on paper or on external storage media, such as a USB flash drive. The parent public key, chain code, and the index number are combined and hashed with the HMAC-SHA512 algorithm to produce a 512-bit hash. The right-half 256 bits of the hash output become the chain code for the child.
- They depend on the same Elliptic Curve Cryptography and Secure Hash Algorithm as any other address.
- To help cut down on confusion a new BCH address format was introduced called the “cash address” format .
- Click the Deposit button next to the cryptocurrency you want to find out the wallet address for.
- Meanwhile, on another, more secure server, the extended private key can derive all the corresponding private keys to sign transactions and spend the money.
- Otherwise, hard wallets are the best to store digital assets for longer periods.
For example, during the recovery process, you may be prompted to enter the 2nd, 3rd, 7th 10th, and 12th words in the seed phrase through your selected Bitcoin wallet software. A Bitcoin address is a more efficient way of representing a Bitcoin public key. Just like any other public key cryptosystem, the Bitcoin network uses asymmetric encryption. This is just a fancy way of saying that the network enables users to generate and use private-public key pairs.
The left-half 256 bits of the hash and the index number are added to the parent private key to produce the child private key. In Figure 4-11, we see this illustrated with the index set to 0 to produce the 0’th child of the parent. In bitcoin, most of the data presented to the user is Base58Check-encoded to make it compact, easy to read, and easy to detect errors. The version prefix in Base58Check encoding is used to create easily distinguishable formats, which when encoded in Base58 contain specific characters at the beginning of the Base58Check-encoded payload. These characters make it easy for humans to identify the type of data that is encoded and how to use it.
How to get my wallet address to deposit crypto?
Branches of keys can also be used in a corporate setting, allocating different branches to departments, subsidiaries, specific functions, or accounting categories. Both what is a bitcoin address private and public keys can be represented in a number of different formats. These representations all encode the same number, even though they look different.
Without the child chain code, the child key cannot be used to derive any grandchildren either. You need both the child private key and the child chain code to start a new branch and derive grandchildren. So what happens if you somehow forget your password to a non-custodial wallet? Instead of being able to reset your password via an email account, you will need to use a seed phrase in order to regain access to your funds.
Vacation season: How to travel safely with cryptocurrencies
You never do anything with it consciously, but it is used to sign your transaction when you send crypto assets. The wallet address format depends on the respective blockchain, but it usually consists of around https://xcritical.com/ 25 to 40 alphanumeric characters and includes numbers, letters and sometimes even special symbols. These key pairs allow to share the public key which can be used by others to encrypt or verify information.
Sometimes called a mnemonic phrase, a seed phrase is a list of random and unique words that is generated whenever you create a non-custodial wallet. You should write down the seed phrase and store this information in a secure place. Unless you use a desktop or hardware wallet, there is very little chance that you have ever had access to your private key. Online Bitcoin wallet services, including those offered by exchanges such as Coinbase and Kraken, tend to give users only a receiving, public address. Due to the security implications of a user misplacing their wallet’s private keys, it’s easy to see why wallet services restrict their users from accessing them.
How to Choose the right Cryptocurrency to Trade or Invest in
Some basic knowledge about crypto wallets is necessary to understand how a Bitcoin blockchain address works. Although it is possible to repeatedly use individual receiving addresses generated in your account, this practice is not recommended as it can link payment data to one individual. Trezor Suite generates fresh addresses for each transaction, although for Ethereum you’ll need to add another ETH account. By generating a fresh address each time, you reduce the chance of exposing any sensitive personal information. Some wallets can pair and connect to a hardware wallet in addition to being able to send to them.
The mnemonic code represents 128 to 256 bits, which are used to derive a longer (512-bit) seed through the use of the key-stretching function PBKDF2. The resulting seed is used to create a deterministic wallet and all of its derived keys. Bitcoin addresses are derived from a public key using a one-way function.

Some new hardware wallets come with the ability to connect to your device through Bluetooth. Use these with caution because Bluetooth is a wireless signal that can be accessed by unwanted parties when it is turned on. For someone who follows the ‘single-use token’ concept, they may have discarded that address and the corresponding private key because they weren’t expecting to re-use it. That’s why it’s crucial to make sure that the recipient is able and willing to receive funds sent from a previously-used address. Now that we’ve covered the basic definitions required for Bitcoin transactions, there are a few concepts you should understand about sending and receiving BTC.
The Keys to Crypto Kingdom: Wallet Address, Public and Private Keys Explained
Each key must be backed up, or the funds it controls are irrevocably lost if the wallet becomes inaccessible. This conflicts directly with the principle of avoiding address re-use, by using each bitcoin address for only one transaction. Address re-use reduces privacy by associating multiple transactions and addresses with each other. A Type-0 nondeterministic wallet is a poor choice of wallet, especially if you want to avoid address re-use because that means managing many keys, which creates the need for frequent backups. Although the Bitcoin Core client includes a Type-0 wallet, using this wallet is discouraged by developers of Bitcoin Core. Figure 4-8 shows a nondeterministic wallet, containing a loose collection of random keys.
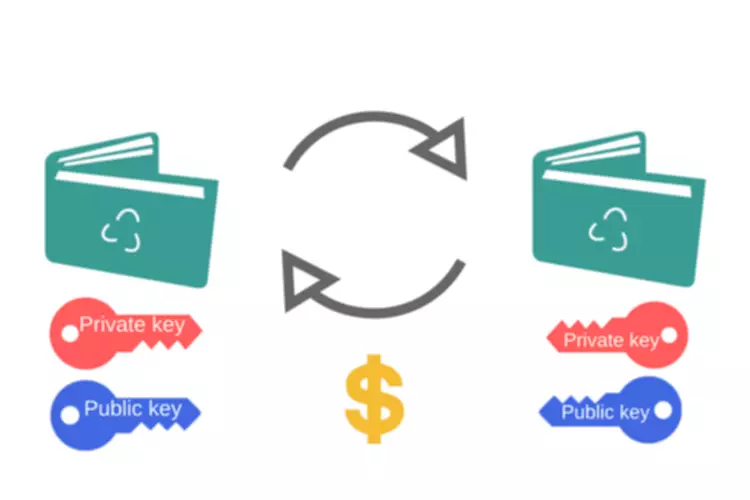
People can send the cryptocurrency to Bitcoin addresses similarly to the way fiat currencies can often be sent to email addresses. However, the Bitcoin address is not intended to be permanent, but just a token for use in a single transaction. Unlike a digital wallet, a Bitcoin address cannot hold a balance. A private key is a secret number that is used to send encrypted messages. The safest crypto wallet has no connection on its own or to a device with internet access. It also should not deny you access to your crypto because the custodian has financial issues.
Since both Bitcoin Cash and Bitcoin are irreversible payment systems, there is no way to reverse a sent transaction, or for you to recover bitcoins from your end. If you are purchasing bitcoins for a specific reason, please confirm if you require BCH or BTC before proceeding with your purchase. To replicate your BNB wallet’s address, click the duplicate icon in the “Address” column. After logging in to Binance, select “Wallet” from the top menu button, and then select “Fiat and Spot (Deposits & Withdraw)” from the drop-down menu. Tables 4-6 and 4-7 show some examples of mnemonic codes and the seeds they produce.
Core Functionality
While the exact steps to find it heavily depends on what Bitcoin software you use, most wallets will have a “Receive” section with the address clearly visible and ready to be copied. Put simply, an address is a group of arbitrary digits and letters that represent a given user’s Bitcoin balance. The owner of a wallet can also choose to send or receive bitcoin to other users as many times as they like, using their own address as the source. A Bitcoin address is used to identify who the owner of a particular amount of bitcoin is. When a new Bitcoin wallet is created using a piece of software, an address is also randomly generated. Since the wallets you control are capable of receiving funds from external blockchain sources, you are able to generate an address for your wallets by using the create address endpoint.
A data dictionary is a collection of descriptions of the data objects or items in a data model to which programmers and others can refer. Completing the CAPTCHA proves to us that you’re a human and gives you access to our platform. You can find more information on the AppCoins Wallet, including how to install it by visiting this post.
This can help you keep track of your payments as well as maintaining a higher level of privacy. As well as protecting your privacy, using a fresh address greatly reduces the risk of losing incoming funds or sending them to the wrong address. In public blockchains, such as Bitcoin, it is possible to see all transactions that have been made on a particular address by looking into a blockchain explorer. Almost all full nodes help the network by accepting transactions and blocks from other full nodes, validating those transactions and blocks, and then relaying them to further full nodes.
As secure as a hardware wallet sounds, using it is cumbersome and time inefficient. You have to connect it to a device and enter security keys each time you make a transfer. The entire procedure is much more complex than web or software wallets, which require just a few clicks. In a transaction, the spender and receiver each reveal to each other all public keys or addresses used in that transaction. This allows either person to use the public blockchain to track past and future transactions involving the other person’s same addresses.
What is a Crypto Wallet?
On the fourth level, “change,” an HD wallet has two subtrees, one for creating receiving addresses and one for creating change addresses. Note that whereas the previous levels used hardened derivation, this level uses normal derivation. This is to allow this level of the tree to export extended public keys for use in a nonsecured environment. For example, the Bitcoin Core client pregenerates 100 random private keys when first started and generates more keys as needed, using each key only once. This type of wallet is nicknamed “Just a Bunch Of Keys,” or JBOK, and such wallets are being replaced with deterministic wallets because they are cumbersome to manage, back up, and import. The disadvantage of random keys is that if you generate many of them you must keep copies of all of them, meaning that the wallet must be backed up frequently.
Cryptocurrency Wallet: What It Is, How It Works, Types, Security
If you forget your wallet password, regaining access to funds is quite easy. You can think of this sort of as a Bitcoin account, rather than a pure wallet. You would just go through the typical password reset steps through email as you would for most other online accounts. However, there are potential security risks involved with trusting someone else to manage your private keys. For example, if a wallet provider’s database suffers a security breach, private keys may be compromised.
You give yours to others to receive payments and ask others to send theirs when making a transfer to them. Now your wallet is all set up to deposit Bitcoin or any other crypto assets, but for that, you will need a Bitcoin blockchain address. If you wish to use it on your mobile phone, you can find optimized applications of the most popular web-based and software wallets for Android and iOs both. For desktop, some wallets, such as MetaMask, provide a browser extension, while others, like Atomic and Exodus, require you to download their applications. However, you must know that you’re taking some big risks by keeping your holdings in these wallets. There have been several incidents in the past where the entire exchange system got breached, and hackers swept away users’ funds.

